Malware analysis Malicious activity
4.8
$ 36.00
In stock
(480)
Product Description
Malware Analysis Guide: Types & Tools
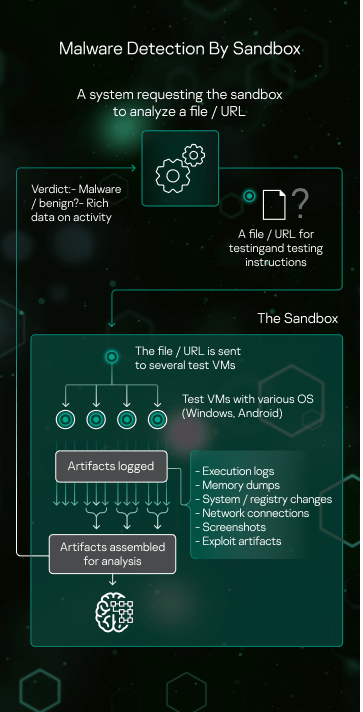
Sandbox Kaspersky

What is Malware Analysis
MALWARE DETECTION : EVASION TECHNIQUES - CYFIRMA

Intro to Malware Analysis: What It Is & How It Works - InfoSec Insights
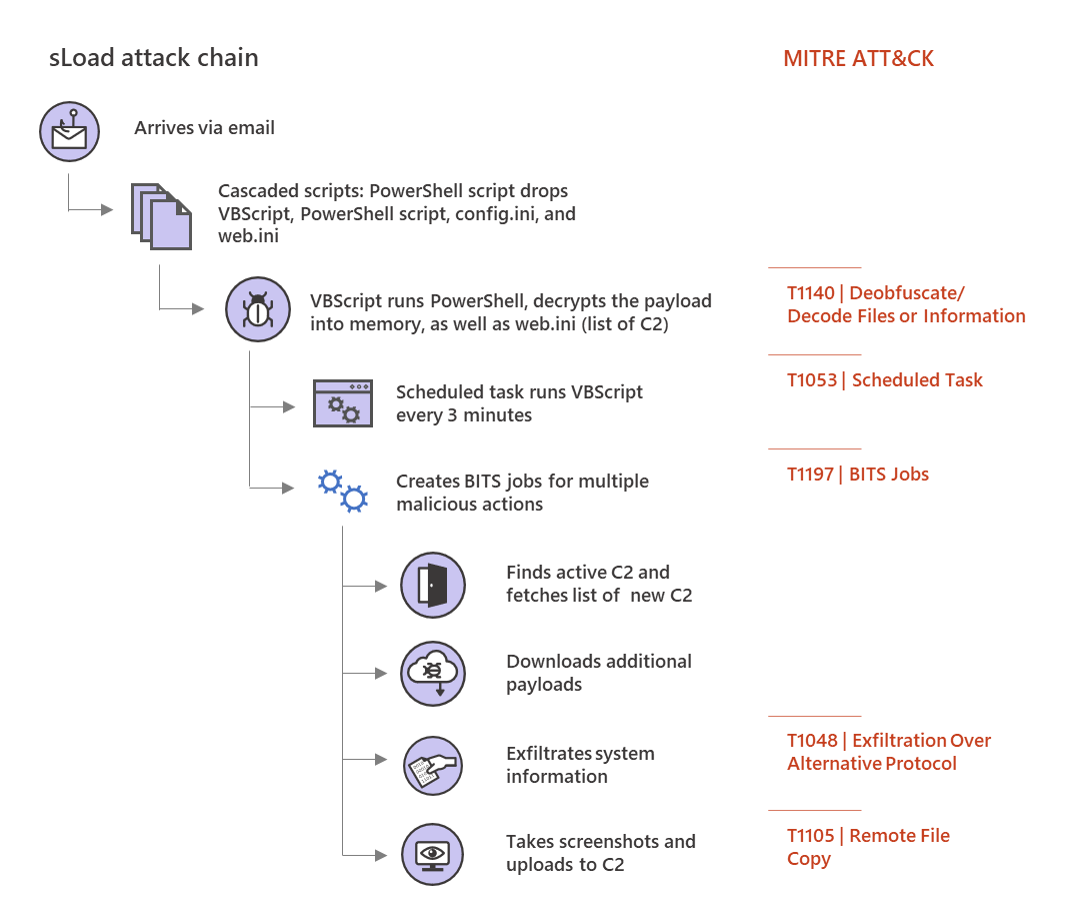
Multi-stage downloader Trojan sLoad abuses BITS almost exclusively for malicious activities
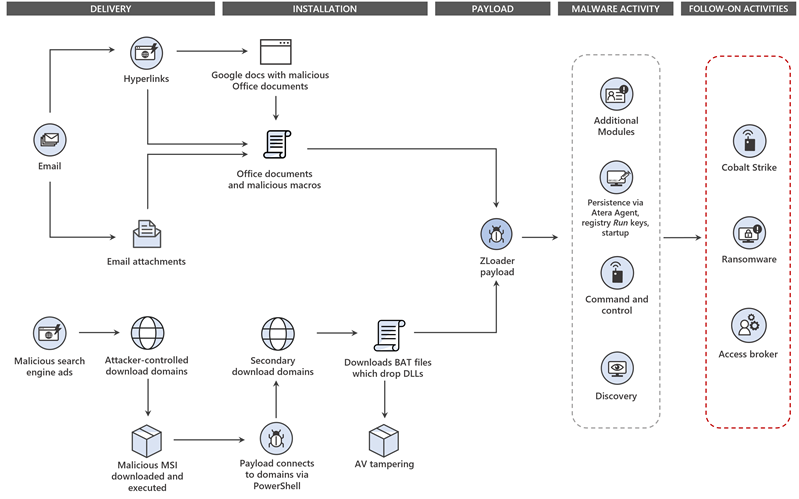
Dismantling ZLoader: How malicious ads led to disabled security tools and ransomware
11 Best Malware Analysis Tools and Their Features
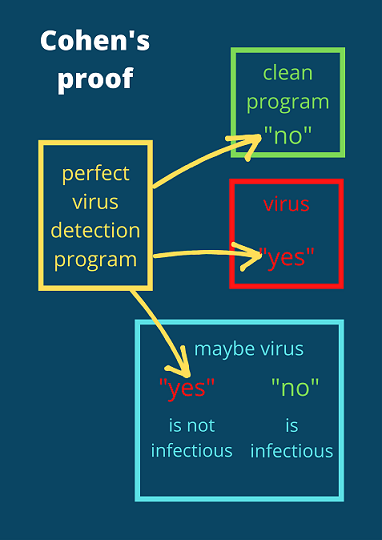
The real reason why malware detection is hard
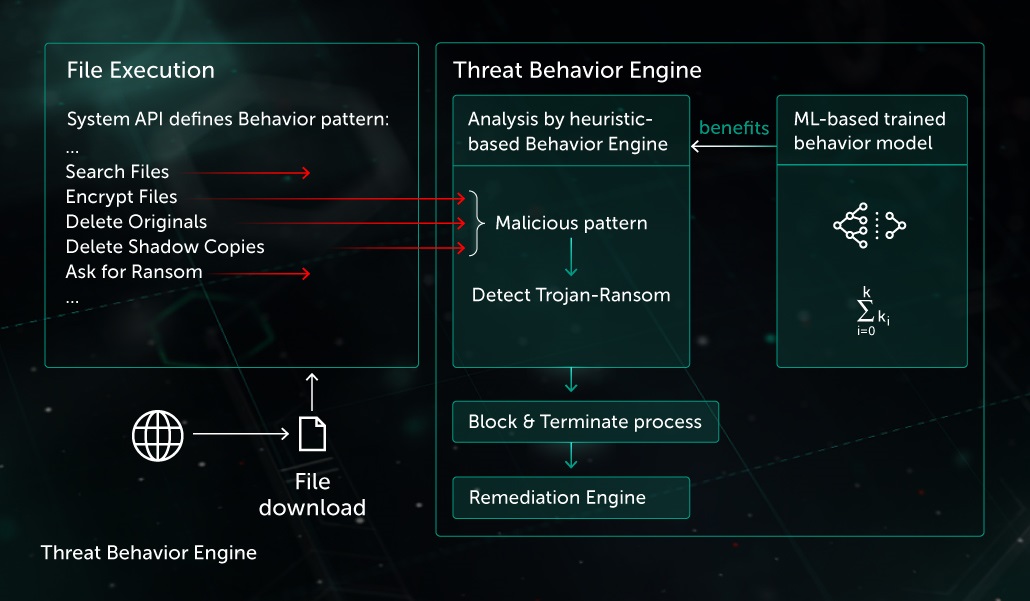
Behavior-based Protection

Intro to Malware Analysis: What It Is & How It Works - InfoSec Insights
Symmetry, Free Full-Text

Malicious Excel Document Malware Analysis, by Jay Vadhaiya